We use messages all the time to communicate. Even in the era of the internet, they still reign. Apart from the usual communication, there are situations where hacking texts become inevitable.
If you know that your kid is vulnerable to bullies, you will want to hack his or her phone. The same case applies when you are investigating an issue at the workplace. If you are in a fix that needs text messages hacking, then we have a solution for you.
It’s an app that will hack the SMS’ without notifying the targeted user. If you are asking how this is possible, stay tuned to find out.
Now, one of the best ways to access other people’s text messages is to install an app like eyeZy.
A monitoring app allows you to see everything that’s going on on someone else’s phone. Every message sent and received is sent to your dashboard. And when messages are deleted, you can still see them thanks to tools like Keylogger and Screen Logger.
EyeZy also includes a tool called Social Spotlight. You can also access their social media chats on apps like WhatsApp, Snapchat, Messenger, and others.
If your goal is to keep kids safe, eyeZy is your best choice. For one purchase you get everything you need, as well as many tools you didn’t even know you had.
Part 1: Hack Text Messages without Them Knowing with Cocospy
From research, we can comfortably say that this is a beast application in the spying niche. The Cocospy monitoring solution has already helped millions of people to fulfill their hacking objectives.
It is a large package that is full of hacking tools. One of them is the ability to fetch messages from a targeted phone remotely. Cocospy is indeed quiet. It has the stealth mode feature to hide its icon during operation.

That means your target will know nothing until you complete or decide to stop the hacking. In text messages, Cocospy gets you everything you need to know. It will show you whatever was sent or received, the contact details, and the time too.
All this happens in real-time. Therefore, you will not have to wait for the messages to sync. They will be available on your end as soon as the target sends or receives something. When it comes to phone platforms, Cocospy will hack both Android and iOS phones.
In the latter, it hacks even the deleted iMessages. The best part is that it does not need any rooting or jailbreaking to get started. Do you want to know about other apps that don’t demand such tricks? Check how to hack text messages solution.
In Android, Cocospy demands a one-time installation on the targeted phone. After that, you can hack online via your established account. That means you will not need the phone again. In Apple devices, Cocospy does not require any download or installation.
It uses the iCloud ID of the targeted phone to hack the text messages. Once you have it, the only thing remaining is registering an account and verify the iCloud login details online.
In both phone platforms, the hacked messages are shown to you via a user-friendly web-based dashboard. It has other features as well that you need to peruse. It’s fully compatible with all browsers. So, you can use any internet-enabled device to check on the results.
The dashboard uses a secure cloud to relay the information. Cocospy, however, does not store any of the fetched data in its cloud. So, you are the only one who can access the hacking updates.
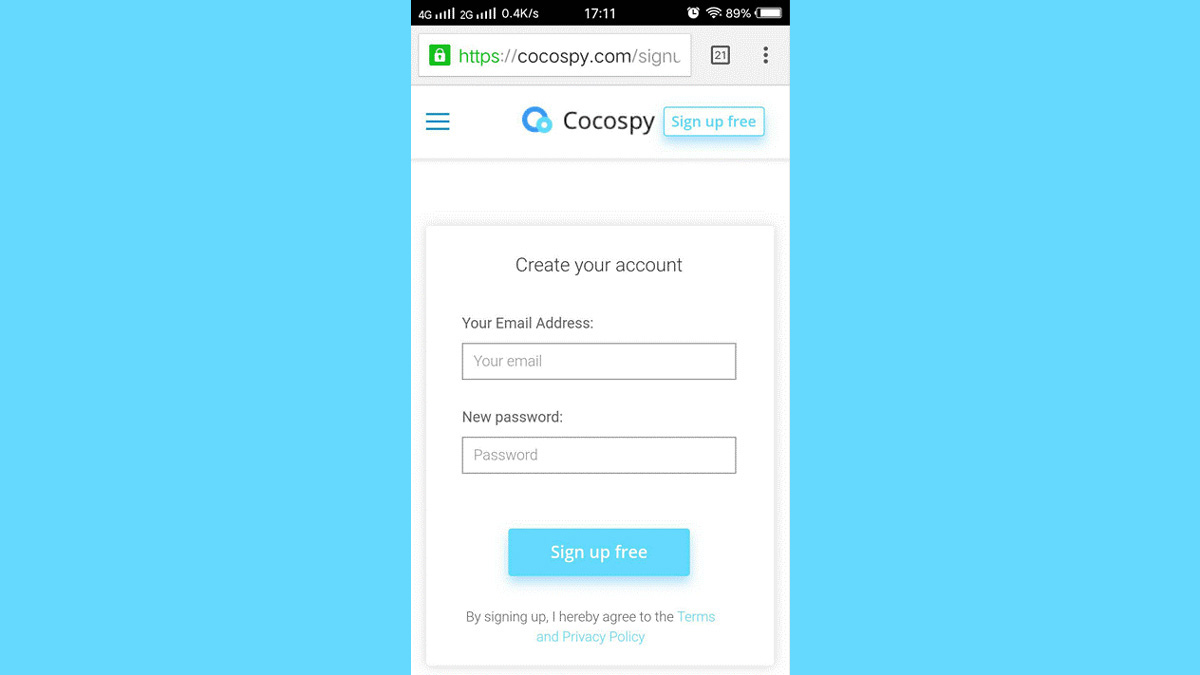
To use Cocospy, you can register an account via the main website or with Clickfree. Here are the requirements and steps to start hacking messages with this application.
Part 2: How to Start Hacking Text Messages Using Cocospy
What You Need
- In Android, you need the targeted phone to install Cocospy. Make sure it has OS version 4.0 or above.
- In iOS, get the target’s iCloud details. The iPhone/iPad should have iOS version 7.0 or later.
- Reliable internet connection
- A valid email address
Steps to Start Hacking
Step 1: Visit the Cocospy website and register an account. Next, select the targeted phone’s OS to continue to the next page.
Step 2: Choose the best hacking plan and proceed to make the payment. You will immediately receive a confirmation email with the receipt, log in details and the setup instructions. In Android, you will also get a download link.
Step 3: For Android, use the sent link to install Cocospy on the targeted phone. Make sure you activate stealth mode. After that, finish up the installation and login to your account using another device.
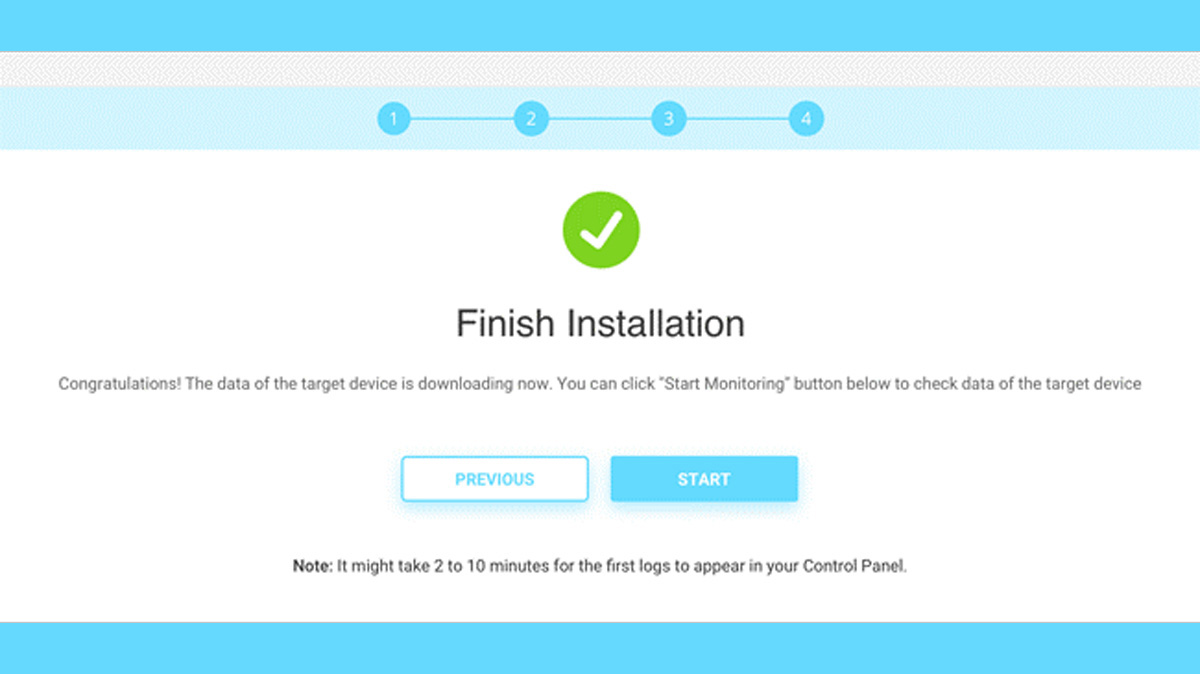
Step 4: For iOS, after the confirmation email, login to your account remotely and verify the target’s iCloud credentials. Next, select the device you want to hack and wait for the Cocospy and iCloud synchronization.
Step 5: After re-accessing your account, you will see the dashboard after a few minutes of syncing. What you should be interested in are the features on the left menu.
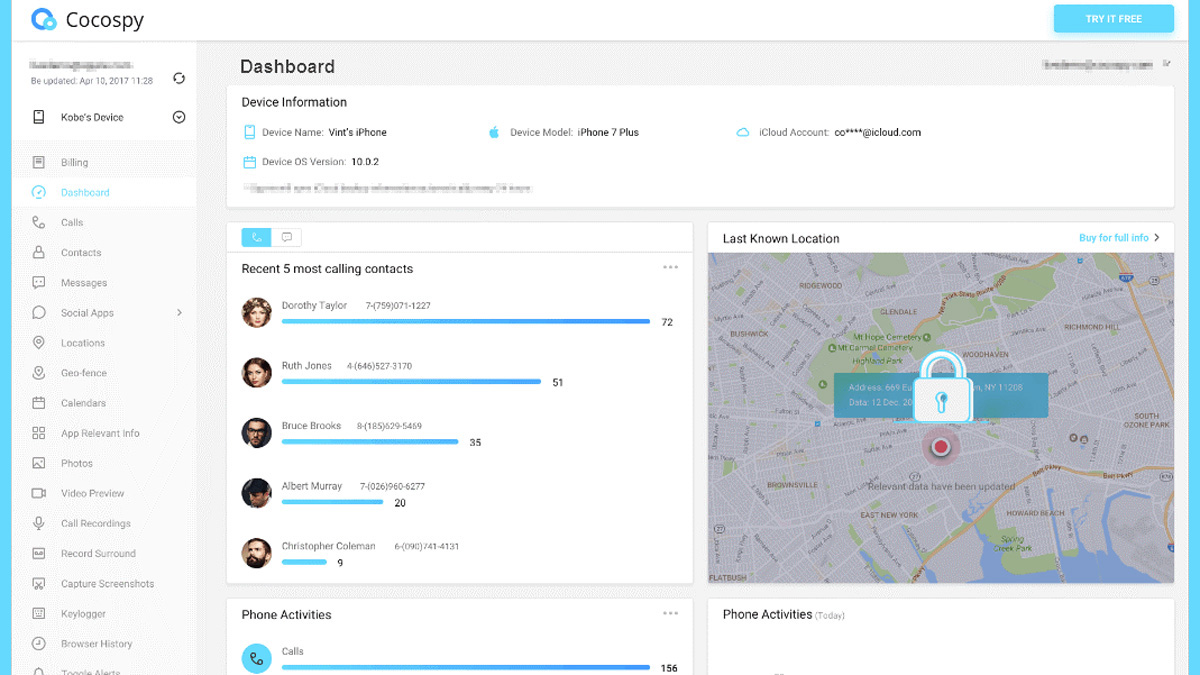
To hack the messages, click on Messages and iMessages options to see what Cocospy has captured for you.
Part 3: Cocospy Text Hacking Benefits
You may have already seen other apps boasting the same. However, this is what makes Cocospy win:
- It takes less than 5 minutes to set it up
- Cocospy does not demand to root or jailbreak whatsoever
- Real-time hacking results regardless of where you are
- It uses stealth mode to hide its icon. In iOS, it uses the iCloud to hack. That means your target will never know despite what the phone they are using
- Cocospy does not drain the battery when hacking the messages
- In Android, it uses less than 2MB memory space
- You can uninstall Cocospy remotely via the online control panel. So, you don’t have to access the targeted phone physically to remove it
Cocospy has other hacking features worth exploring. It can hack the call log, contacts, location, and social media activities. Visit the demo page to see all the elements in action.
Conclusion
It’s effortless to hack text messages without alerting the targeted phone user. On the other hand, it takes the right solution with the right tools and mechanisms to do so.
We recommend Cocospy since it’s easy to use, requires minimal steps, and gives results in real-time. It also does not demand to root or jailbreak, which are some of the things that can notify the target.
Do you have any questions about hacking text messages or the Cocospy application? Leave a comment below, and we will not hesitate to respond.


How do I get started?
Nice article, Please I want to hack my husband deleted text messages, access to his call.
You write very good article.
Thanks for this nice article. I will try this method.
I have tried this technique. It is effective. Thanks a lot.